Data Center Decommissioning: A Complete Guide to Certified Green Destruction
When hardware reaches end-of-life in a data center, the decommissioning decision carries consequences that extend far beyond the loading dock. Data center decommissioning services touch three domains that matter simultaneously to infrastructure and compliance teams: data security, environmental regulation, and ESG accountability. A poorly managed decommissioning project exposes the organization to GDPR or LGPD breach risk, WEEE non-compliance, and untracked Scope 3 emissions. A well-managed one produces auditable chain-of-custody records, certified IT asset disposal documentation, and measurable sustainability metrics that feed directly into ESG reporting.
This guide covers what a complete decommissioning process involves, which certification standards to require, how to navigate the regulatory landscape, and what to look for when evaluating a certified green decommissioning provider.

What Data Center Decommissioning Actually Involves
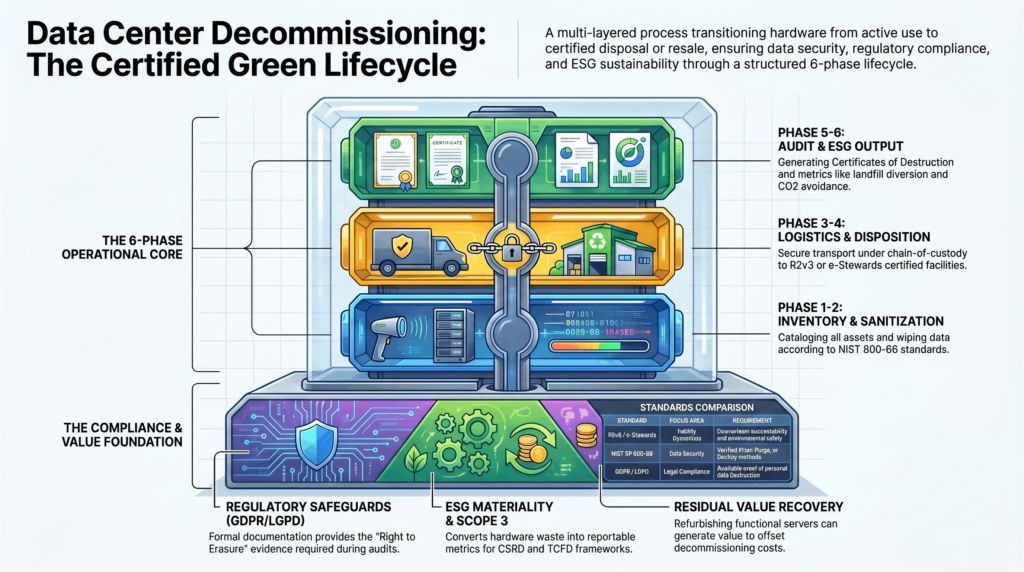
Many organizations conflate ‘decommissioning’ with ‘server removal.’ In practice, data center decommissioning services span a structured lifecycle that begins long before hardware is physically touched and ends long after it leaves the facility. Getting this scope right is the difference between a compliant, auditable process and a liability.
At a minimum, a complete decommissioning engagement includes: a full asset inventory (serial numbers, model, data classification), data sanitization verified against a recognized standard, physical asset removal and transport under chain-of-custody protocols, downstream disposition (refurbishment, resale, or certified recycling), and documentation packages including Certificates of Destruction and environmental reporting for ESG disclosures.
The 6-Phase Decommissioning Process
Phase 1 — Asset Discovery and Inventory: Every device in scope is catalogued with physical and logical attributes. This phase often surfaces undocumented assets that create compliance risk if missed.
Phase 2 — Data Classification and Sanitization: Data on each device is assessed against its classification (confidential, regulated, public) and sanitized to the appropriate standard—NIST 800-88 Clear, Purge, or Destroy—with verification and Certificate of Destruction issued per asset.
Phase 3 — Physical Disassembly and Logistics: Hardware is removed from racks, labeled, manifested, and transported under chain-of-custody protocols that document custody at every handoff.
Phase 4 — Certified Disposition: Assets are routed to certified recyclers (R2v3 or e-Stewards) or prepared for resale/refurbishment. No landfill-bound material leaves without documented disposal verification.
Phase 5 — Documentation and Audit Package: The organization receives a complete documentation package: asset-level Certificate of Destruction, recycling certificates, chain-of-custody manifests, and environmental metrics.
Phase 6 — ESG Reporting Output: Recycling weight, landfill diversion rate, CO2 equivalent avoided, and component recovery data are compiled for ESG disclosure and sustainability reporting.
Certification Standards That Matter in Decommissioning
Not all decommissioning providers are created equal—and certification is the primary mechanism for distinguishing legitimate ITAD compliance from marketing claims. Two international standards define best practice:
R2v3 (Responsible Recycling): The R2v3 standard, managed by SERI (Sustainable Electronics Recycling International), covers the full ITAD lifecycle including data sanitization, worker health and safety, environmental management, and downstream vendor accountability. R2v3 is the most widely required certification in enterprise ITAD contracts in North America and internationally.
e-Stewards: Developed by the Basel Action Network, e-Stewards is the more restrictive of the two major certifications—it prohibits export of e-waste to developing countries and imposes stricter environmental controls. For organizations with strong ESG commitments or operating in sectors where social responsibility standards are scrutinized, e-Stewards provides the higher bar.
For most enterprise decommissioning programs, R2v3 is the minimum requirement. For organizations with formal ESG commitments, dual certification (R2v3 + e-Stewards) or e-Stewards alone provides the strongest claim.
Data Sanitization: NIST 800-88 and Beyond
Data sanitization is the most legally consequential phase of certified IT asset disposal. The applicable standard depends on the sensitivity classification of data on each device:
NIST SP 800-88 Clear: Logical overwrite techniques sufficient for non-sensitive data. Appropriate for devices that will be reused internally.
NIST SP 800-88 Purge: Cryptographic erase or block erase for media that will leave organizational control. Required for most enterprise decommissioning scenarios.
NIST SP 800-88 Destroy: Physical destruction (shredding, disintegration) for media containing classified or highly sensitive data where Purge cannot be verified.
For U.S. federal and defense contractors, DoD 5220.22-M remains a referenced standard, though NIST 800-88 is now the NIST-recommended approach. For organizations subject to GDPR or LGPD, the key requirement is verifiable, documented destruction—the specific technical method is secondary to the chain-of-custody and Certificate of Destruction output.
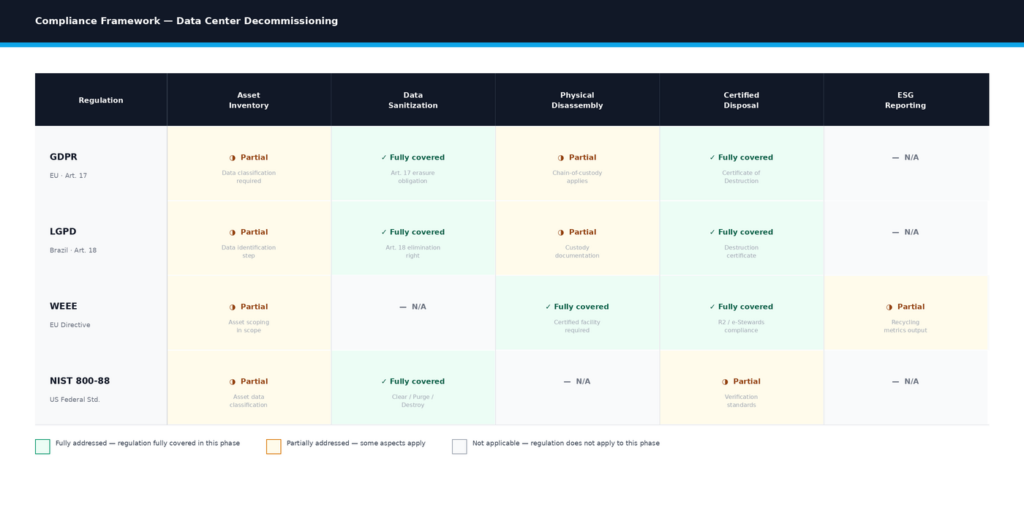
Regulatory Compliance and Legal Exposure
The regulatory landscape for hardware disposal is multi-layered and jurisdiction-specific. Compliance failures carry financial penalties, but more importantly, they create discoverable evidence of negligent data handling.
GDPR (EU) and LGPD (Brazil): Both frameworks require that personal data be destroyed securely when no longer needed. Article 17 of GDPR (Right to Erasure) and Article 18 of LGPD create affirmative obligations that extend to hardware disposal. A Certificate of Destruction from a certified IT asset disposal provider is the documentary evidence required to demonstrate compliance during an audit or breach investigation.
WEEE Directive (EU): The Waste Electrical and Electronic Equipment Directive requires that e-waste be handled by certified facilities. Organizations that dispose of hardware outside the WEEE framework—even informally—expose themselves to penalties and reputational risk.
RoHS: The Restriction of Hazardous Substances Directive affects how hardware containing restricted materials (lead, mercury, cadmium) must be processed. Certified recyclers maintain RoHS-compliant processing chains.
For organizations operating across jurisdictions, ITAD compliance requires a provider who understands the applicable framework in each geography and produces documentation that satisfies all relevant regulators. A single Certificate of Destruction format rarely satisfies all jurisdictions without adaptation.
| Standard / Regulation | Scope | Key Requirement | Document Output | Applicable Regions |
| R2v3 | ITAD operations | Data sanitization, downstream chain, worker safety | R2 Certificate | Global (SERI-accredited) |
| e-Stewards | ITAD operations | Stricter environmental controls, no developing-country e-waste export | e-Stewards Certificate | Global (BAN-accredited) |
| NIST SP 800-88 | Data sanitization | Clear / Purge / Destroy by media type | Certificate of Destruction | US (federal reference) |
| GDPR Art. 17 | Personal data on retired hardware | Documented erasure / destruction of personal data | Certificate of Destruction | EU + adequacy countries |
| LGPD Art. 18 | Personal data on retired hardware | Right of elimination; documented destruction | Certificate of Destruction | Brazil |
| WEEE Directive | E-waste processing | Certified facility handling; landfill diversion | Recycling Certificate | EU + aligned countries |
| DoD 5220.22-M | Classified / sensitive data | Multi-pass overwrite (superseded by NIST 800-88) | Certificate of Destruction | US federal / defense |
| ISO 14001 | Environmental management | Environmental management system at facility level | ISO 14001 Certificate | Global (voluntary) |
Want a structured framework for your next decommissioning project? Request our Decommissioning Process Checklist — a 20-point audit document covering all phases from asset inventory to ESG reporting output.
ESG and the Business Case for Green Decommissioning
The ESG case for certified green data center decommissioning services has shifted from optional to reportable. Under frameworks like GRI (Global Reporting Initiative), TCFD, and the EU Corporate Sustainability Reporting Directive (CSRD), organizations are required to disclose material environmental impacts—including those in their Scope 3 emissions footprint. Hardware disposal is a Scope 3 Category 12 (end-of-life treatment of sold products) or Category 5 (waste generated in operations) item, depending on asset ownership structure.
Certified green decommissioning produces the metrics that satisfy these reporting requirements: total weight recycled, landfill diversion percentage, materials recovered (gold, silver, copper, palladium from circuit boards), and CO2-equivalent avoided versus landfill disposal.
Beyond compliance, there is a tangible financial upside. Refurbishment and resale of functional equipment—servers, storage, networking hardware—can generate meaningful residual value. Certified ITAD providers who combine green destruction with asset remarketing can return value that offsets the cost of the decommissioning engagement itself.
How to Evaluate a Decommissioning Services Provider
When selecting a certified IT asset disposal partner, the checklist goes beyond certification. Key evaluation dimensions include:
Certification currency: R2v3 or e-Stewards certificates should be current—not lapsed, not pending renewal. Verify directly with SERI (R2) or the Basel Action Network (e-Stewards).
Scope of data sanitization: Confirm that NIST 800-88 Purge or Destroy is standard—not an add-on. Request sample Certificates of Destruction to assess format and completeness.
Chain-of-custody documentation: Every handoff—from your facility to the ITAD facility, from the ITAD facility to downstream recyclers—should be documented with manifests, GPS tracking, or equivalent.
Downstream accountability: Ask who the provider’s downstream recyclers are and whether they are also R2v3 or e-Stewards certified. A certified provider using uncertified downstream vendors negates the certification.
ESG reporting package: For organizations with ESG disclosure obligations, confirm that the provider produces a structured environmental metrics report, not just a weight ticket.
Insurance and indemnification: Verify that the provider carries adequate errors and omissions (E&O) and environmental liability insurance, and understand your indemnification rights in the event of a data breach post-disposal.
Decommissioning Readiness Framework: Before You Begin
Use this checklist before engaging a data center decommissioning services provider to ensure organizational readiness.
Score: 0 = Not addressed | 1 = In progress | 2 = Complete
- Asset inventory: Is a complete device-level inventory in place (serial numbers, model, data classification per device)?
- Data classification: Are all devices classified by sensitivity level (public, internal, confidential, regulated)?
- Regulatory mapping: Have applicable regulations been identified for each asset’s data content and jurisdiction?
- Provider certification: Has the provider’s R2v3 or e-Stewards certification been verified as current?
- Sanitization method: Is the data sanitization method (Clear / Purge / Destroy) specified per device class in the SoW?
- Chain-of-custody: Is a chain-of-custody documentation process agreed with the provider before work begins?
- Certificate of Destruction format: Has the format and content of the Certificate of Destruction been reviewed and approved for audit use?
- ESG metrics: If ESG reporting is required, has the provider confirmed the format and content of the environmental metrics output?
- Residual value: Have assets been assessed for refurbishment or resale potential before scheduling destruction?
- Downstream verification: Has the provider disclosed and documented their downstream recycling partners?
Score 0–10: High-risk decommissioning posture. Complete foundational steps before engaging a provider.
Score 11–15: Moderate readiness. Address open items before work begins.
Score 16–20: Well-prepared. Proceed with provider engagement and formalize remaining items in the SoW.
Common Pitfalls in Data Center Decommissioning
Treating certification as a binary checkbox. R2v3 or e-Stewards certification is necessary but not sufficient. Certified providers with inadequate downstream controls, outdated processes, or uncertified subcontractors can still produce compliance failures. Verify the full chain, not just the top-level certificate.
Skipping the asset inventory phase. Organizations that begin physical decommissioning without a complete asset inventory routinely discover undocumented devices mid-project—storage arrays with regulated data, networking devices with embedded credentials, end-of-lease assets that complicate ownership. The inventory phase is a prerequisite, not an option.
Assuming NIST 800-88 is universal. NIST 800-88 is a U.S. federal reference standard. For organizations subject to GDPR or LGPD, the regulatory requirement is documented, verifiable destruction—not a specific technical method. Using NIST as the organizational standard is defensible in most jurisdictions, but verify with legal counsel before assuming compliance.
Separating data sanitization from certified IT asset disposal. Some organizations use internal IT teams for data wiping and then pass hardware to an ITAD vendor for disposal. This creates a chain-of-custody gap and a documentation gap. For regulated data, the sanitization and disposal process should be managed by the same certified provider under a continuous chain of custody.
Underestimating ESG reporting requirements. Organizations that engage a decommissioning provider and receive only a weight ticket discover—when ESG reporting season arrives—that the documentation is insufficient for disclosure frameworks. Specify ESG reporting output requirements in the SoW before work begins.
Best Practices for Certified Green Decommissioning
Integrate decommissioning into hardware lifecycle management from day one. End-of-life disposition should be planned when hardware is procured, not when it fails. Lifecycle tracking systems that flag hardware approaching end-of-life enable planned decommissioning rather than reactive disposal—reducing cost, reducing risk, and improving ESG metrics.
Specify data sanitization by device class in the SoW. A single blanket data sanitization specification is insufficient. Specify NIST 800-88 Purge for storage media leaving the organization’s control, Destroy for devices with classified or highly sensitive data, and document the method per-device in the Certificate of Destruction.
Require ESG reporting output as a contractual deliverable. For organizations with sustainability reporting obligations, the environmental metrics from a decommissioning engagement—recycling weight, landfill diversion, materials recovered—belong in the SoW as a required deliverable, not a request made after the fact.
Conduct a residual value assessment before scheduling destruction. Functional hardware that is certified-destroyed at end-of-life rather than refurbished and resold represents lost value. A pre-decommissioning assessment of market value for each asset class can significantly offset the cost of the engagement.
Audit the provider’s downstream chain at least annually. For ongoing ITAD programs, annual audits of downstream recycling partner certifications are the most effective way to prevent compliance drift. Require your ITAD provider to produce downstream partner certifications on request.
Conclusion
Data center decommissioning services have evolved from a logistics problem into a compliance and ESG accountability function. The organizations that treat hardware end-of-life as a strategic process—not a one-time event—build a repeatable capability that satisfies regulatory requirements, produces audit-ready documentation, and generates sustainability metrics that matter for reporting.
The framework is clear: certified provider (R2v3 or e-Stewards), NIST 800-88-compliant data sanitization, full chain-of-custody documentation, and structured ESG reporting output. The checklist for organizational readiness is defined. The common pitfalls are avoidable.
What remains is execution—and the selection of a certified IT asset disposal partner whose process, documentation, and downstream accountability match your regulatory and ESG obligations.
Ready to start your decommissioning project the right way? Request our Decommissioning Process Checklist — a 20-point guide covering every phase from asset inventory to Certificate of Destruction and ESG reporting output.
Frequently Asked Questions
What does a complete data center decommissioning services engagement include?
A complete engagement covers six phases: asset discovery and inventory, data classification and sanitization (per NIST 800-88), physical disassembly and logistics under chain-of-custody protocols, certified disposition (R2v3 or e-Stewards recycling or refurbishment), documentation (Certificate of Destruction, recycling certificates, chain-of-custody manifests), and ESG reporting output (recycling weight, landfill diversion, materials recovered).
What is the difference between R2v3 and e-Stewards certification?
Both are internationally recognized ITAD certifications, but e-Stewards is generally considered the more stringent standard. R2v3 (Responsible Recycling, managed by SERI) covers the full ITAD lifecycle including data sanitization and downstream accountability. e-Stewards (from the Basel Action Network) additionally prohibits the export of e-waste to developing countries and imposes stricter environmental controls. R2v3 is the more common requirement; e-Stewards is preferred for organizations with strong ESG or social responsibility commitments.
What is NIST 800-88 and why does it matter for decommissioning?
NIST Special Publication 800-88 (Guidelines for Media Sanitization) defines three levels of data sanitization: Clear (logical overwrite for internal reuse), Purge (cryptographic or block erase for hardware leaving the organization), and Destroy (physical destruction for classified or high-sensitivity data). It is the U.S. federal reference standard for data sanitization and is widely used internationally as the baseline for certified IT asset disposal. For GDPR and LGPD compliance, NIST 800-88 Purge or Destroy provides defensible evidence of data destruction.
Do I need a Certificate of Destruction for every decommissioned device?
For devices that processed or stored personal, confidential, or regulated data, yes. A Certificate of Destruction provides the audit evidence required under GDPR (Article 17), LGPD (Article 18), and various sector-specific regulations (HIPAA, PCI DSS, SOC 2). For non-sensitive devices (network switches with no data storage, dummy load units, etc.), the level of documentation may be reduced — but document the decision in the SoW to maintain a defensible audit trail.
How does decommissioning relate to ESG and Scope 3 emissions reporting?
Hardware disposal is a Scope 3 emissions item under the GHG Protocol (Category 12: end-of-life treatment of sold products, or Category 5: waste generated in operations). Certified green decommissioning produces the metrics required for ESG disclosure: recycling weight, landfill diversion percentage, materials recovered, and CO2-equivalent avoided versus landfill disposal. Organizations subject to GRI, TCFD, or EU CSRD frameworks need this data to complete their environmental disclosures. Uncertified disposal produces none of it.
What is chain of custody in ITAD, and why does it matter?
Chain of custody is the documented transfer of physical asset control at each handoff in the decommissioning process — from your facility to the ITAD provider’s truck, from the truck to the processing facility, from the processing facility to downstream recyclers. Each transfer is documented with manifests, asset lists, and signatures (or equivalent electronic tracking). Chain-of-custody documentation is the primary mechanism for demonstrating that hardware did not leave the certified process — which is the question regulators ask when a data breach is traced to improperly disposed hardware.
Can decommissioned hardware generate financial return?
Yes. Functional hardware at end-of-life — servers, storage arrays, networking equipment — may have significant resale or refurbishment value, particularly if less than 5–7 years old. A certified ITAD provider who combines green destruction with asset remarketing can assess market value per asset and route functional units to secondary markets. This residual value can offset or, in some cases, exceed the cost of the decommissioning engagement. The key is assessing value before scheduling destruction.
What regulations apply to hardware disposal under GDPR and LGPD?
GDPR Article 17 (Right to Erasure) and LGPD Article 18 establish obligations to delete or destroy personal data when no longer necessary. For hardware disposal, this means verified, documented destruction of any data stored on the device. A Certificate of Destruction from a certified IT asset disposal provider, referencing the sanitization method and the specific device, is the standard documentary evidence for demonstrating compliance during audits or breach investigations.
What is the WEEE Directive and how does it affect data center decommissioning?
The Waste Electrical and Electronic Equipment (WEEE) Directive is EU legislation requiring that electrical and electronic equipment be collected, treated, and recycled by certified facilities rather than disposed of in landfill or via unauthorized channels. Data centers decommissioning hardware in the EU must ensure that equipment is directed to WEEE-compliant recyclers. Using non-certified disposal channels — even for cost reasons — creates regulatory exposure and may void insurance coverage for environmental liability.
How do I verify that a decommissioning provider’s certification is current?
For R2v3 certification, verify directly through SERI’s certified company directory at sustainableelectronics.org. For e-Stewards, verify through the Basel Action Network’s certified recycler directory at e-stewards.org. Never rely solely on the provider’s self-reported certification documentation — certification can lapse between audits, and a lapsed certificate negates the compliance claim. Verify before signing a contract, and consider a verification clause that triggers re-verification before each engagement.
What should a decommissioning SoW include?
A complete SoW should specify: scope of assets (by type, quantity, and location), data classification per device class and corresponding sanitization method (NIST 800-88 level), chain-of-custody documentation requirements, Certificate of Destruction format and timing, downstream partner disclosure requirements, ESG reporting deliverables (format, metrics, timing), residual value assessment and disposition authority, financial terms (cost and any residual value sharing), insurance requirements, and SLA for project completion.
Is informal or DIY data wiping sufficient for regulatory compliance?
Generally no, for regulated data. While NIST 800-88 Clear-level wiping is technically performable with free tools, regulatory compliance requires documented, verifiable destruction with a Certificate of Destruction issued by an accountable party. Internal IT teams performing data wiping cannot typically produce the independent, auditable Certificate of Destruction that GDPR, LGPD, and sector-specific regulations require. For hardware containing regulated personal data, engaging a certified IT asset disposal provider is the defensible approach.